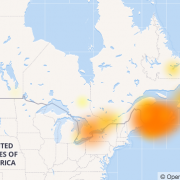
If you were in Eastern Canada or trying to connect with someone in the region for work or pleasure on August 4th, you might not have succeeded for a period of three hours or so. While this event was NOT tied to a cybersecurity breech or issue, there are three cybersecurity lessons that we can learn from the Internet Outage in Eastern Canada.
One service provider, Bell, confirmed this week that it was a perfect storm of the work of construction crews -unrelated to Bell’s operations – not checking for cables prior to digging that resulted in service to internet, mobile and landlines being impacted. This outage also impacted emergency services in much of Atlantic Canada. (Another good reminder for construction crews to call before you dig.) Bell’s customers were not the only ones affected. Telus, Koodo and Virgin customers also had interrupted services. Thankfully they took action quickly and remedied the situation as quickly as possible.
So, other than an extreme inconvenience to customers, there are some observations we can make from this experience. This outage can really help people think what would happen if there was a major cybersecurity attack in Canada. This is something good to come out of this outage – getting people thinking about what-if scenarios.
1. Our Economy Depends on the Internet
I feel like this should be a no brainer, but at the same time I do want to reinforce this thought. We typically have such reliable internet services that we don’t give it a second thought. If anything, this outage should have really pounded home the fact that a cyberattack could not only have the same affect, but the likely hood that it would only last a few hours, is slim to nil. The affects would be long-lasting.
This outage impacted not just consumers of these service providers, but businesses in general. If your business relies on the internet for online sales or providing support services, your customers, regardless of where they are located were not able to purchase your products or services for hours. They also were not able to get online support services from you. If they went old school and tried to call you, they were also out of luck. In some cases, this might be enough for potential customers to go to your competitors.
What if you were delivering online training to customers around the globe on that fateful Friday? People who had paid and signed up weeks prior were then either dumped from the online course and/or could not sign-in.
Finally, this was a long weekend in Canada. Imagine people travelling and wanting to make last minute hotel accommodations. What happens when they can’t get through to you? Or, what happens when their car breaks down on a highway somewhere and they can’t use their phone for hours to call for help? This was the middle of summer and warm. What would happen if this was the middle of January in Eastern Canada?
These are all very real scenarios that could happen as a result of a cybersecurity attack.
2. Our Safety Depends on a Safe and Resilient Internet
I am fairly certain there were people who dialled 911 or other emergency service numbers on the 4th that were quite alarmed when they could not actually reach help. Whether it is hours or minutes, time matters in an emergency!
3. Security and Privacy, Backup Systems and Processes Must be Baked-In at the Beginning of all Systems
We must never underestimate security, privacy, backup systems and processes being what we call “baked-in” at the beginning of any system development. All new systems must be created with these critical elements a part of the planning, development and execution process.
It is critical to note that this has not always been the case. It’s not that it was left out intentionally, but older systems could have been built at a time when cybersecurity breaches were not the reality. That being said, it is very much our reality now. As a result, all businesses and governments must now revisit and update their systems to ensure that these critical elements are baked-in going forward.
Eastern Canada has been fortunate to have good systems in place run by leading companies. This outage however, was definitely – or should definitely be – a wake-up call for us all to revisit cybersecurity measures to ensure that we protect our citizens and our economy. After all, we need a safe and resilient internet in order to operate our businesses, our emergency services and live life the way we have all become accustomed too.
Cybersecurity is a critical issue that we all face now. If you are interested in learning more about communications protocols around cybersecurity and privacy breeches, get in touch with us.