Is LinkedIn the Next Tool for Super Spam?
Remember the email from a certain part of the world that offered us millions of dollars if we helped some widow or bank employee get unclaimed money out of the country? Or, more recently how about those super annoying calls from people that claim to be calling from California because they somehow know that our computers are either not working properly or have been hacked? Of course the best part of the call is that if we give them control of our computers they can fix it for us…ya, you know what I am talking about. I found it ironic that some of these crafty souls moved from email to telephone, but now I fear that they have found a new medium: LinkedIn. In fact, I can’t help but wonder if LinkedIn is the next tool for super spam.
I really hope not. I love LinkedIn. I think that it is a very well done social network for professionals. It has been a very effective tool for networking and engaging with industry experts for me, as well as countless others. Let’s hope that what I am noticing is just an anomaly, and that the spammers haven’t found a way to ruin it. That being said, there are some ways that you can be on the look out for potential spammers; and some best practices that I adhere to, which will also help to deter spammers:
1. Make Strategic Connections – It’s Not A Numbers Game
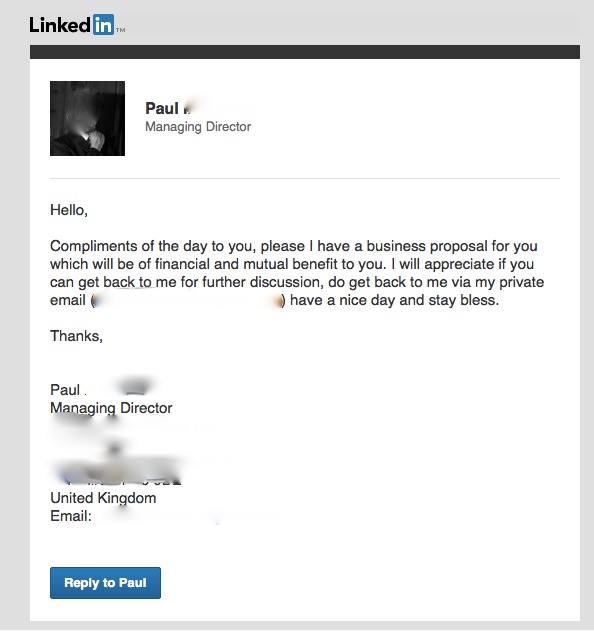
A sample of a request I received. This LinkedIn profile no longer exists. I would say that the spammers were shut down.
While some argue that you should connect with everyone who asks, I am not one who prescribes to this. LinkedIn is an important networking tool and like in real-life, you don’t invite everyone into your private or semi-private life. You want to build a relationship.
When I make connection requests, I do so carefully. Equally as important is who I accept connection requests from. I don’t automatically press “accept”. To the contrary! I check out each person. If I have met the person, that is one criteria for acceptance. If I have not actually met the person, but I am in the same geographic region or industry, I will likely accept. The probability is increased when we have mutual connections.
If however, I have never met the person, we are not in the same geographic location in the world, we are not in the same industry and we have no mutual connections, there is a very good chance that I won’t accept.
Key Take-Away: Focusing on your industry and mutual connections is a great way to help get the spammers at bay.
2. Play Investigator
If your goal is to increase your numbers, or if you don’t feel comfortable pressing the “ignore” button, do play investigator. Take a look at the person connecting with you. Does the avatar look real? Or, does the quality seem a bit off. While this can’t be a guarantee that someone has set up a fake profile, potentially using someone else’s photograph, it is a symptom. Google the person and the company that he or she claims to work for. Can you find the company? Better yet, can you find any reference for that person connected to the company?
What is the message that is being sent? Is it one offering you a financial deal and/or benefit? Like the phoney email sent offering you huge sums of money, this is yet another scam.
Is the person asking you to contact him or her via email to act upon this deal? What is the email being used. Is it a company email? Is it a gmail? Is it a hotmail account?
Depending on how you answer these questions, you should also have a good indication about the validity of the request.
Key take-away: don’t be afraid to check out the person requesting to connect. After all, this is your professional network and you want quality connections – and no spam.
3. Take Your Time
Again, if you are not comfortable pressing ignore, but are suspect, wait a few days. I recently got a request that not only offered me a financial deal, but the avatar was a bit wonky and I couldn’t find any reference to the company and/or the person when I did a search. I did hit ignore and ultimately the spam feature, but kept the request for use in the blog post that I was going to do. As I was writing this post, I thought that I would do one more check. Sure enough, the profile is no longer available. Enough people saw the request for what it was and answered like I did. The person or persons was shut down.
Key take-away: being timely is important as it speaks to your personal brand; however, if you are uncertain about a particular request, waiting a day or two might result in action already occurring to fix the issue.
With a bit of due diligence we can keep the spammers at bay.
Want to learn even more? Sign up for our newsletter at TaylorMade Solutions (insert “newsletter” into inquiry box)
